What Are The Security Risks Of Cloud Computing? – Cloud computing is changing day by day and with the introduction of more companies the need for security is increasing.
Cloud Security refers to a set of management-based technologies designed to secure and protect data, data security and all related applications.
What Are The Security Risks Of Cloud Computing?
Security operations also include backup of data and business operations so that data can be recovered even in the event of a disaster. The cloud computing process handles the security controls provided by the network provider to protect its data and privacy.
Cloud Computing Fundamentals: Risk Management
Cloud Computing provides storage to organizations and businesses to store and process data. There are many services that an organization can use for their needs.
Some of the services are Software as a Service, Platform as a Service, and Infrastructure as a Service. There are two main broad types of Cloud Computing security issues:
Cloud related problems provided by cloud providers can be solved with the help of tools. Cloud providers must continuously monitor this so that customers do not face any obstacles.
However, the customer must also take responsibility for managing and protecting data in the cloud. The company is equally responsible for the security and privacy of information. The customer can also protect the data with the help of strong passwords and authentication measures.
Cloud Security Solution
In the cloud, there is a risk that the data can be obtained by an unauthorized user, because it can be found wherever it is necessary to stop it by verifying the identity of the user. Strong certification and approval should be a priority.
The cloud can reach anywhere and thus lead to increased risk. With a large number of users accessing the cloud, the risk is very high.
Therefore, the connectors used to manage public cloud resources must be protected as well as their integration with remote access and web browser vulnerabilities.
The customer must be informed about any delay caused by all subsequent reporting and management of security incidents. So there must be a good system and the customer must know the truth.
Cloud Security Risks, Threats, And Best Practices
The level of security is high and the same level of security should be provided for many services deployed in cloud services. There must be administrative supervision in the matter of distributed work
Personal information of customers should be protected as it is one of the most important aspects. Data availability can be a big problem for consumers and suppliers.
This problem can increase quickly in relation to the transfer of a lot of information which will lead to lack of clarity of information and will lead to great losses.
There are several steps and systems for building cloud security that can be found in the following categories:
How Secure Is Your Cloud Storage? Mitigating Data Security Risks In The Cloud
This type of control helps reduce attacks on cloud systems. This program reduces the risk, but does not actually eliminate the risk. It also prevents unauthorized access so that the privacy of the cloud is not compromised. As a result, cloud users are known.
Please write a way to manage the attack list in the cloud system by providing an alert level that lowers the third level by notifying an authorized person. If there is unauthorized access, it displays a warning message that there will be negative consequences if it continues without stopping.
These controls detect the event. In the event of an attack, researchers will inform the user to repair and fix the problem.
This control reduces the effects of the event by stopping the damage. It also resets and restores the system to make everything work properly.
Categorizing Web Hosting Business For State Filing: A Guide
All safety measures are appropriate if the use of safety measures is taken correctly. Cloud infrastructure should detect problems and come up with solutions as soon as possible.
II. There must be an overview of the data and the data must be stored in different places.
Encryption is a service provided by the administrator where the data is encrypted and after encryption it is stored in the cloud. This is an important part of cloud security and can be very useful.
Safety is important and cannot be taken for granted. The choice of IT professionals is the private cloud over the public cloud. That’s why we canaa cloud security plays an important role in the cloud industry.
Cyber Detect Pro
Assessment of cloud computing security issues – Journal of Internet Services and ApplicationsCloud Computing is a flexible, cost-effective and proven platform for providing IT for businesses or consumers… jisajournal.springeropen.com
Printing architecture and configuration in Windows Server 2012 R2 The Windows printing architecture consists of a set of print drivers and a basic part of the printing interface known as print…
AWS VS AZURE VS GCPIt is a common fact that cloud computing is increasing in importance and popularity. A Gartner report predicts that in the year 2020,…
Linux operating system Linux is an open source platform. The OS finds a host between applications and devices, and creates connections between all your…
Top Saas Security Risks And How To Mitigate
Building productive AI applications has never been easier. From modeling workflows to RAG-based applications, Amazon SageMaker Canvas offers unparalleled code democratizing capabilities. …
Review of ‘Adblock Professional for Youtube’ ExtensionAuthors: Berkay Aksaray, Emre Durmaz, Fatih Çelik, Tufan Güngör — — — — — — — — — — As Trendyol Security team …
A Pentester’s Approach to Kubernetes Security — Part 1 This is the first of a two-part blog series based on the vulnerabilities we commonly identify during the Kubernetes Penetration tests we perform…
Microsoft Entra ID: reveal the future of Cloud Identity and Access Management ) and the organization that uses the service. It is important to review this from the beginning to understand the complex topic of cloud security that we are about to enter.
Review The Top Risks Of Cloud Computing
Cloud Computing has brought many benefits. Easy access to data from anywhere in the world, rapid deployment of applications, and low operating costs are just a few of the long list. Therefore, it is not surprising that the market continues to expand.
According to a Fortune Business Insights report, the cloud computing market grew by $108.64 billion last year and is expected to reach $2,432.87 billion by 2030. Keep in mind that those figures are only for North America.
As always, all good things come with a downside. Or several. Wherever there is a lot of money and sensitive information, criminals gather, waiting for the right moment to launch an attack. So, let’s go ahead and see exactly what the types of cloud computing risks are and how they can be mitigated. To begin, we will take a look at the most commonly used types of cloud environments.
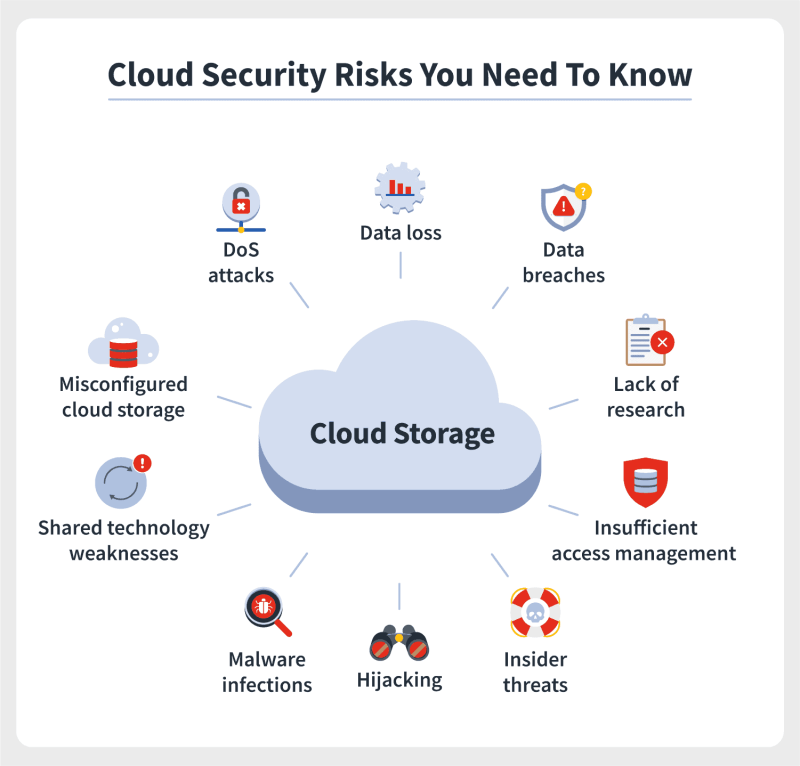
As beneficial as cloud computing is, it also comes with some security risks, which can lead to data loss and security exposure.
What Are The Top Security Risks In Cloud Computing?
Incorrect settings and incorrect cloud security practices are one of the main causes of cloud data loss. Threat actors use unsecured cloud resources as a gateway to access passwords, financial information, phone numbers and all kinds of sensitive information.
Companies often have reduced visibility and control over the cloud resources they use. In this case, it is the cloud service provider (CSP) that is responsible for configuring and maintaining its cloud resources. However, security teams must review and adjust the default settings, which are often too permissive.
Below is a short list of things that are often misconfigured and pose a risk to cloud security:
Operational visibility refers to the ability to monitor, track, and understand activities, events, and behaviors within a cloud computing environment. When you move workloads to the public cloud, you lose many of the systems you had on-premises.
What Are The Security Risks Of Cloud Computing? Explained
Lack of visibility into cloud resources and operations leads to an inability to detect threats and respond effectively. Unfortunately, you cannot access the data packets traveling through the cloud, so you cannot control the information they contain. Lack of operational visibility also affects forensic investigations.
Poor access control management, compromised data and vulnerabilities in network resources or applications can lead to unauthorized access to critical data. Breaches can result in data theft, financial loss, reputational damage, and non-compliance with data protection laws.
Personally identifiable information (PII) is of particular importance to actors. After collection, they will try to sell the data on the dark web to other adversaries interested in identity theft and phishing attacks.
Sensitive documents and e-mails of a well-known company are often used to damage the company’s reputation or affect the price of its stock.
Cloud Security Risks And Cautiousness Of Cloud Computing
This is a particular risk in a public cloud environment, where many organizations share the same infrastructure. If a customer’s system or data is compromised, it can also compromise the security of other customers. Multi-tenancy essentially expands the attack surface. If the CSP fails to ensure proper segregation between tenants, the risk of data leakage increases.
Also, vulnerabilities in the CSP’s infrastructure, such as hypervisor or virtualization vulnerabilities, can pose risks to the security of the entire environment.
Many organizations use the cloud for data storage. In addition, it is a common practice to run internal and customer-facing software in the cloud, especially when working remotely.
Of course criminals know and want to exploit that. So, they started Denial or
Top 5 Security Risks Of Cloud
Assessing the security risks of cloud computing, what are the security risks of the cloud computing, the security risks of cloud computing, what are the risks of cloud computing, risks of cloud computing, security risks of cloud computing, security risks with cloud computing, security risks cloud computing, the risks of cloud computing, what are the security risks in cloud computing, what are the risks in cloud computing, what are the security risks of cloud computing coursehero