Risks Of Using Cloud Computing – Cloud-based IT environments are now the norm in businesses of all sizes. Security and complexity risks are inherent to the territory, but they can all be mitigated.
COVID-19 has presented unprecedented challenges to organizations of all sizes and backgrounds. But while everything from the economy to operations has taken a nosedive, one area of technology has become strong, resilient and, in many cases, a savior. Cloud adoption has increased steadily during the pandemic and thanks to the inherent benefits of remote working.
Risks Of Using Cloud Computing
In recent years, IT professionals and decision-makers around the world have chosen hybrid cloud as the ideal IT operating model for their businesses, according to a report from Table-Inform Enterprise Cloud. The report is based on a survey of more than 3,400 IT professionals worldwide, 86% of whom consider hybrid their preferred IT operating model.
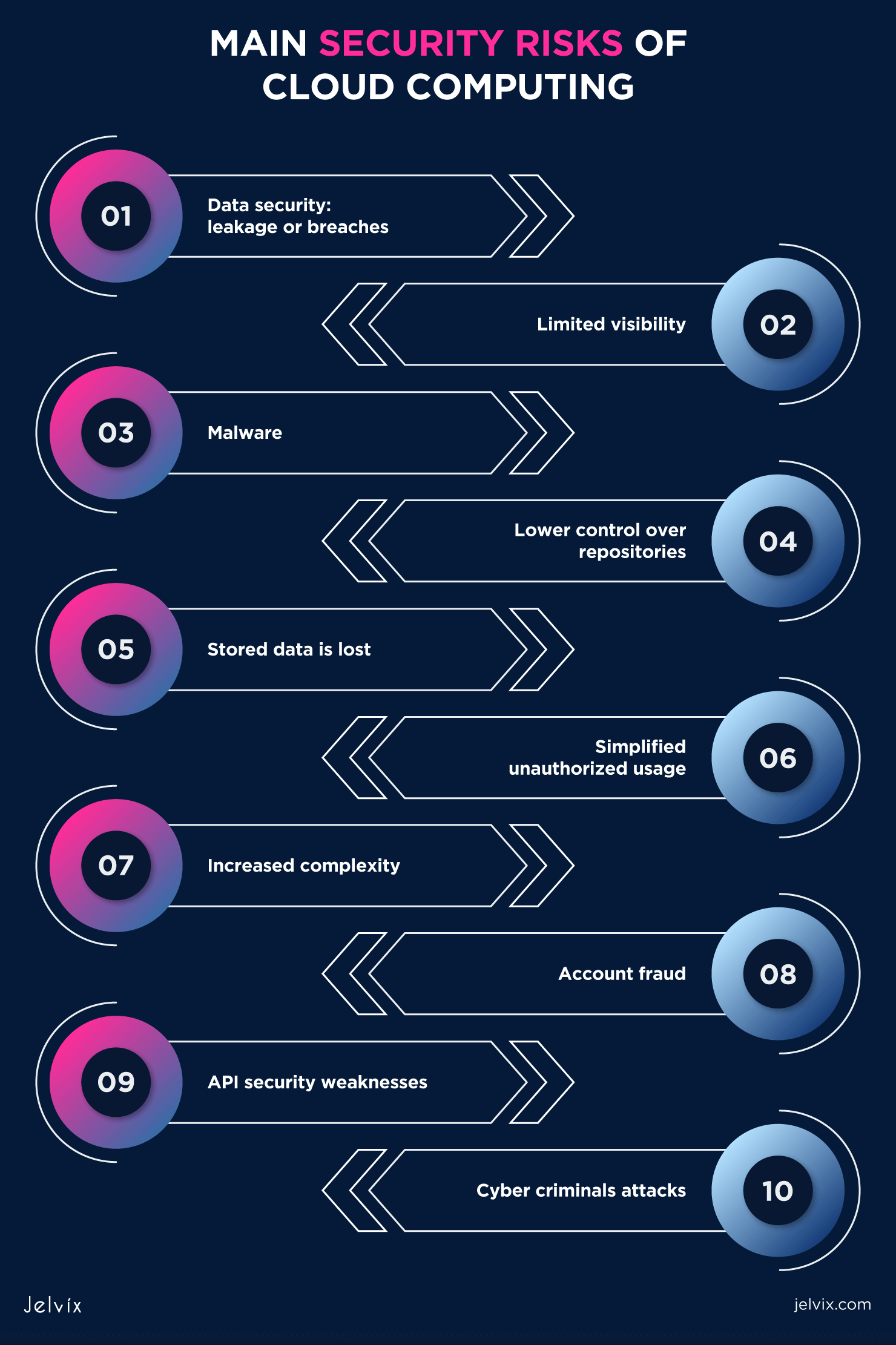
Categories Of Issues And Risks In Cloud Computing
Organizations are increasingly turning to hybrid, multi-cloud environments in the race to improve team productivity, rapidly scale their IT infrastructure, secure their data, reduce operational costs and ultimately create business value.
However, with all this scale, speed and convenience comes some complexity. And complexity breeds danger. As expected, the Flexera State of the Cloud 2021 report reveals that security, consumption and management are the top cloud computing challenges for organizations of all sizes.
Here’s a look at the biggest risks in cloud computing and some ideas on how to manage them as cloud technology continues to grow at a rapid pace.
Unauthorized access to data poses by far the greatest threat to cloud computing, or any IT infrastructure technology, for that matter.
The Impact Of Cloud Computing On Risk Management And Fraud Prevention
For what? Nearly 100% of organizations responding to IDC’s survey reported experiencing at least one cloud data breach in the past 18 months.
Threat actors make money by selling or using employee and customer data, and businesses are data goldmines. Additionally, cloud attacks typically evolve at a much faster pace than security defenses: cyberattacks are increasingly sophisticated, and IT teams face an almost impossible challenge to keep up.
Cloud service providers host the data of hundreds of thousands of people across hundreds of companies. In many cases, the entire cloud is vulnerable to a single point of failure. A successful attack could be fatal for many businesses and their customers around the world.
Be careful: Outsiders are not the only ones who attempt to gain unauthorized access to company data. The insider threats that overshadow cloud-based solutions are equally murky. Malicious, insecure, or careless employees can bypass organizational access controls and upload files to a third-party cloud service without authorization.
Pdf] Cloud Computing Threats And Risks: Uncertainty And Unconrollability In The Risk Socety
Business networks can be further weakened by vendors to whom IT or other functional services are outsourced. In such cases, trust is transferred to their employees as well as other suppliers with whom they subcontract.
Mitigation Strategy: Reducing the risk of unauthorized access to data in the cloud requires comprehensive, integrated, and intensive security planning. Start with a zero-trust security framework that requires all users to be continuously authenticated and authorized for every action they take.
“Organizations are starting to understand that they should not automatically trust anything inside or outside their perimeter. This advantage has been largely erased. So, we now see companies checking everything that tries to connect to their IT systems,” said Amit Bareket, CEO of Perimeter 81.
“With zero-trust security, it’s easy to enforce policies and protect by isolating applications and segmenting network access based on user permissions, authentication, and authorization. By implementing the ZTNA model for secure network access, IT teams can have full control over who can access, enter, and leave the network at any time. This model has gained much more recognition since it was mandated by President Biden’s executive order,” Bareket explained.
Pdf) Cloud Security: Services, Risks, And A Case Study On Amazon Cloud Services
Cloud technology is evolving rapidly. Post-pandemic, more businesses of all sizes are undertaking digital transformation efforts and moving more workloads to the cloud remains fundamental to this change.
Organizations are struggling to keep pace with their operations and adapt to ever-increasing customer demands. The previously mentioned Flexera report also reveals that 92% of enterprises today have a multi-cloud architecture, with four out of five of these being hybrid cloud environments.
A study from GigaOm found that multi-cloud systems will be the norm in small and large organizations by 2025. For now, many companies’ workloads are distributed across clouds as well as data centers on the site.
The danger? Too much complexity. As complexity increases, more skilled workers, more specialist training and a budget for maintenance are required.
Some Common Security Risks Of Cloud Computing
Mitigation Strategy: Like anything else in an organization, adoption and motivation for cloud computing must come from the top.
“The success of cloud adoption and migration depends on your people. Until you focus on the #1 bottleneck in the cloud adoption flow, improvements elsewhere will be just an illusion,” said Drew Firment, senior vice president at A Cloud Guru .
Many industries (including healthcare, finance, law, and telecommunications), as well as government, regulate the work of organizations in their space. These rules cover data, transactions and IT operations, among other business functions.
For example, HIPAA requires all healthcare providers to protect the privacy of patient data. Likewise, PCI-DSS requires all businesses that accept credit cards to protect their customers’ data.
Pdf] The Risks Of Cloud Computing In Accounting Field And The Solution Offers: The Case Of Turkey
Companies operating in these sectors must establish controls and audits over the data storage, transfer and access methods they use. They must also maintain strict availability thresholds while ensuring data backup and recovery. In many cases, it may not be permissible to outsource these functions to a third party or service provider, particularly if that provider is headquartered in another country.
As a result, many businesses cannot use public clouds for critical workloads or data storage. Those that can may need to ensure that the suppliers they rely on maintain a minimum level of compliance. They must have incident response policies and procedures in place, and even then, if a breach occurs at a cloud service provider, the company can still be sued.
One of the goals of using any cloud technology (like any other) is to better control performance, quality and results. When the organization fails to control these operational aspects, it has a direct and detrimental effect on business continuity.
Additionally, an organization relies on a cloud provider to maintain quality of service at all times for its public cloud (or the public cloud components of its hybrid cloud environment). When things go wrong, recovery depends on the speed of the supplier’s actions.
How To Mitigate The Security Risks Of Cloud Computing
Cloud has become one of the key drivers of digital transformation due to the flexibility, availability, scalability, resilience and flexibility it offers businesses. It has enabled the development and adoption of new disruptive technologies that have led to significant changes in business processes, capabilities and even business models.
Such transformations are not without their share of risks. However, these risks can be largely mitigated with a little forethought and planning.
Michael Brenner is a keynote speaker, author and CEO of Marketing Insider Group. Michael has written hundreds of articles for sites such as Forbes, Entrepreneur Magazine and The Guardian and speaks at dozens of leadership conferences each year covering topics including marketing, leadership, technology and strategy commercial. Follow @BrennerMichael. Remote work is becoming increasingly popular for a wide range of reasons. As a result, more and more businesses are relying on cloud-based technology. Cloud computing is widely used in project management, networking and operations.
According to Cybersecurity Ventures, the total amount of data stored in the cloud, which includes public clouds run by providers and social media companies (think Apple, Google, Microsoft, etc.), government-owned clouds and accessible to citizens and businesses, private clouds. owned by medium and large enterprises, and cloud storage providers will reach 100 zettabytes by 2025. That means 50% of the world’s data at that time, compared to about 50% today.
Cloud Risk Mitigation Strategy With Challenges Optimization Of Cloud Computing Infrastructure Model
What are the advantages of cloud computing? And what risks do businesses face when using cloud services? Let’s dive into the details and show you how to protect your business data from the most common cloud computing risks.
A number of organizations are making technological advancements. This is one of the most powerful strategies for staying competitive in today’s crowded industry. Migrating your organization to the cloud will affect many aspects of your organization’s operations.
The cloud has many advantages: from speed and access to the absence of paper documents. Additionally, there are different types of cloud service platforms, each with its own features. There is no doubt that this form of work carries dangers. Let’s consider them and their solutions
The concept of an “intergalactic PC network” can be linked to the beginnings of cloud computing in the 1960s. Major developments in the field of cloud computing took place in the 1970s and 1990s.
Cloud Computing: Benefits, Security Risks, & Mitigations
For example, IBM developed the VM (Virtual Machine) framework in 1972. In the 1990s, several media companies offered their own versions of virtual private systems. Cloud solutions are now divided into three groups based on their intended use: personal, public and private.
For around ten years, virtual machines have been the pillar of computing
Cloud computing using, what are the risks of cloud computing, security risks with cloud computing, cloud computing risks, cloud computing benefits and risks, benefits and risks of cloud computing, risks of cloud computing, companies using cloud computing, risks associated with cloud computing, security risks cloud computing, security risks of cloud computing, benefits of using cloud computing